Have you ever considered the importance of a key policy for employees in your organization? Establishing a robust key control policy not only enhances overall security, but also provides a structured system for managing employee access. In this blog post, we will walk you through the essential steps of crafting a key policy for employees, ensuring that your organization enjoys the benefits of a secure and well-organized access management system.
Key Takeaways
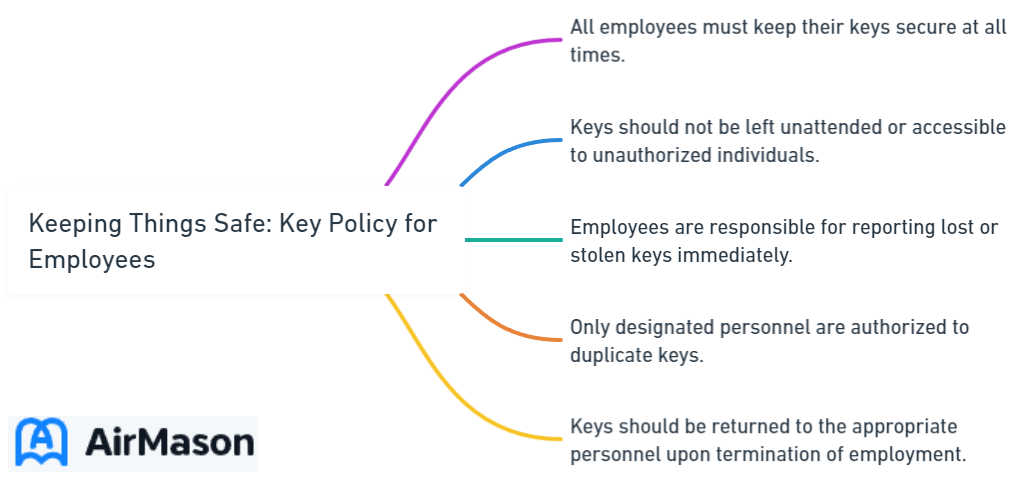
- Establish a Key Control Policy for Employees to ensure security and confidentiality.
- Implement authorization procedures with key custodians formally delegated in writing, build a Master Key System, select patented keying systems and design tiered access structures.
- Monitor & enforce policies by utilizing key tracking software, conducting periodic audits & handling requests/returns online with clear instructions. Ensure timely return of keys through reminders & consequences.
Establishing a Key Control Policy for Employees
A key control policy implementation offers a high degree of security, thanks to a master key system, limited duplication access, and assurance for your company and its employees. The main objectives of such a policy include establishing the protocol for institutional control of keys and outlining the process for requesting keys. A well-crafted key control program ensures stringent accountability for keys issued, ultimately contributing to the overall security of your organization.
Key requests must strictly adhere to the policy’s procedures. These requests should be made using the dedicated key request form. The responsibilities of key holders are crucial in maintaining the security of your organization’s facilities. A comprehensive key control policy will make certain that key recipients safeguard them and avoid leaving them unattended. Proper key management is of utmost importance. Employees terminating their employment must return all keys which have been issued to them prior to departure.
Identifying Employee Access Needs
Identifying and documenting the roles and responsibilities of each employee is fundamental to creating an effective key control system. This ensures that they have the necessary access to carry out their job tasks, including access to master key systems. Determining the access needs for each role is crucial in upholding security and confidentiality.
Organizations can create a system for managing employee access by:
- Establishing authorization procedures
- Building a master key system
- Assigning key holder responsibilities
- Providing training to employees on key control policies
The use of key tracking software, conducting regular audits, employing online forms and procedures, and securing the prompt return of keys can facilitate the implementation and monitoring of this system.
Establishing Authorization Procedures
Managing employee access significantly depends on authorization. The following individuals are authorized to request keys or lock changes within their respective departments:
- Executive Officers
- Department Heads
- Officers of the College
- Designated representatives
These individuals can also make requests for a replacement key. When assuming custody of a master key, individuals must sign a statement affirming their accountability for the care, utilization, and return of the key upon retirement, alteration of position, resignation, or detachment from the organization.
To prevent unauthorized access and duplication, departmental designees should have their authority delegated in writing, on official stationary, with the department head’s original signature. Keys should never be issued to students. Approval of any such request must come from the Executive Officers, Provosts or Vice Presidents.
For the careful management of keys and access, it is essential to develop a different a flexible working hours policy for those entrusted with the keys can also benefit from a structured approach. Employees, like those entrusted with keys, can make requests for adjustments to their work schedules.
However, these requests should follow a clear process, including approval from relevant authorities, to ensure accountability and compliance with company policies. Just as keys should never be issued without proper authorization, flexible work hours should be managed through established channels to maintain the organization’s integrity and security.

Building a Master Key System
A master key system comprises keys that offer varying levels of access to different areas of a facility. Master keys are an essential component of an organization’s security program. Employing a patented keying system prevents unauthorized replication and boosts overall security.
Requiring a card, fob, fingerprint, or other credentials to unlock a door and restrict access based on time, date, and credentials, an electronic access control (EAC) system forms another vital part of an organization’s security program. The audit trail in an EAC system provides a record of every opening or attempted opening of a door, which can be utilized for the investigation of crime and loss.
The mechanical lock serves as a backup mechanism for doors secured by an EAC system. Despite the presence of sophisticated electronic systems, effective key control remains paramount. However, it is important to note that an EAC system can incur a cost of $3,500 for each secured door.
Selecting a Patented Keying System
Your organization can benefit from numerous advantages by opting for a patented keying system. In a patented system, the sale and manufacture of key blanks are regulated by a Federal Utility Patent. This prevents unauthorized duplicate keys and further enhances overall security.
Collaborating with a locksmith who is an authorized dealer of patented key control products is crucial to ensure the implementation of an effective key control policy. A locksmith can confirm identification and record the details of every key they cut, guaranteeing that only authorized persons obtain keys. This level of control over key distribution is invaluable in maintaining the security and integrity of your organization’s access management system.
Designing a Tiered Access Structure
In a master key system, a tiered access structure is indispensable because it provides varying access levels to distinct areas of a facility according to an employee’s role and responsibilities. This type of structure organizes access to resources or information based on different levels of authorization or privilege, dividing users into distinct tiers or levels with each tier possessing distinct levels of access rights.
This structure helps to guarantee that sensitive or confidential information is only available to authorized individuals while permitting others to access the resources they require for their roles or responsibilities.
Implementing a tiered access structure can be achieved by:
- Assigning distinct levels of access rights to various tiers of users
- Assigning different access codes to each tier
- Employing a key control system that allows for various levels of access
A tiered access structure offers enhanced security by confining access to sensitive or confidential information to approved personnel, as well as facilitating more efficient utilization of resources.

Implementing Key Holder Responsibilities
Maintaining a secure environment in your organization necessitates outlining the duties and expectations of key holders. Employees should sign a keyholder agreement to agree to promptly report lost keys and surrender their keys if they depart your employment. The signing of a keyholder agreement is necessary to ensure that all employees promptly report any lost keys and return their keys upon leaving the organization.
The cost of re-keying a lock can be as high as $120. Moreover, the expense of a replacement floor master key is $20 per key, while the cost for a substitute key is $5 per key. It is crucial that incidents of lost keys be reported to the Office of Security and Public Safety.
Signing a Key Holder Agreement
A key holder agreement represents a legally binding contract where an individual is entrusted with the responsibility of safeguarding keys to the organization’s premises. This agreement outlines the rights and responsibilities of the key holder, including the secure keeping and appropriate utilization of the keys, as well as any repercussions for misuse or loss of the keys. It is designed to protect the organization’s assets and guarantee the safety of the premises.
Without patent protection for keys, the policy will have no efficacy. Safeguarding the organization’s assets is of utmost importance to guarantee the security of the premises and to prevent any unauthorized use or disappearance of the keys.
Reporting Lost or Stolen Keys
Notification should be provided to the applicable department or individual responsible for key management within the organization, such as the security department, facilities management, or the key administrator, when a key is lost or stolen. The precise location where the keys were lost or stolen, the exact date and time of the incident, and any other pertinent information should be provided when reporting a lost or stolen key.
The purpose of completing such a report is to:
- Document the loss or theft of the keys, as well as any related access codes or cards, and any potential security risks.
- Suggest rekeying the affected areas or changing the locks to prevent unauthorized access when a key is lost or stolen.
- Adhere to any supplementary protocols in place for notifying of lost or stolen keys to ensure a prompt and appropriate response when a key is misplaced or taken.

Training Employees on Key Control Policies
To ensure that personnel understand the new policies, expectations, and procedures established by the organization, staff training on key control policies is necessary. By understanding how the new program is beneficial to the safety of all, employees will be more accommodating to the policies.
Key control training sessions should encompass all new regulations, expectations, and processes established by the organization.
Conducting Regular Training Sessions
Holding regular training sessions can ensure that employees are apprised of essential control policies and procedures, as well as optimal practices for key utilization. Employees should be aware of:
- The proper use of keys
- The areas in which they are authorized to access
- The procedure to request new access
- The process for obtaining additional access
A keying chart, a visual representation of the hierarchy of keys, can be beneficial in implementing staff training plans.
Reinforcing the Importance of Security
Maintaining a continuous dialogue regarding security is essential in order to guarantee that employees comprehend the significance of security and the optimal practices for strengthening it. This assists in guaranteeing that employees are taking the required measures to safeguard the organization’s data, systems, and networks.
The most effective methods for emphasising the significance of security include:
- Administering regular security awareness training
- Enforcing stringent password policies
- Implementing multi-factor authentication
- Consistently updating and patching software
- Establishing stringent access controls
- Performing security audits
- Promoting the reporting of security incidents
- Routinely communicating about security
- Cultivating a culture of security.
Monitoring and Enforcing Key Control Policies
For maintaining a secure environment, determining who is authorized to access keys, instituting limits on the number of keys issued, and establishing procedures for requesting and returning keys, it’s necessary to establish clear policies. Policies can be effectively conveyed to employees through training sessions, key holder agreements, and other forms of communication.
Implementing key control measures, such as utilizing a patented keying system, establishing a tiered access structure, and employing key tracking software, helps maintain security and prevent unauthorized access.
Refer to our employee rules and regulations sample to establish a comprehensive framework for managing various aspects of workplace conduct, including policies related to key management. This resource can serve as a valuable reference in creating guidelines and procedures that align with your organization’s goals and requirements related to security of information or materials.
Utilizing Key Tracking Software
Key tracking software is a powerful tool that allows organizations to:
- Monitor and regulate the utilization of physical keys
- Provide a centralized system for documenting key information
- Track who has access to certain keys
- Keep records of when keys are checked out or returned
- Document any incidents or issues associated with key usage
This software assists in enhancing security, accountability, and efficiency in key management processes.
Key tracking software may be employed to monitor who has access to particular keys, when keys are checked out or returned, and any incidents or issues associated with key utilization. This assists organizations in guaranteeing that keys are only utilized by authorized personnel and that they are returned promptly. In the event of a lost or stolen key, key tracking software can be utilized to promptly determine when a key has been lost or stolen, enabling organizations to take prompt action to safeguard the premises.
Conducting Periodic Audits
It’s critical to conduct periodic audits to validate key inventory and ensure adherence to key control policies. Establishing clear objectives, planning and preparing for periodic audits, and carrying out a risk assessment during regular audits are the suggested procedures for planning and preparing for periodic audits. Ensuring that the audit team is not subject to any external influences is essential for preserving independence and objectivity when conducting periodic audits.
It is recommended that policies be reviewed and updated on a regular basis in order to ensure that they remain current and are reflective of the organization’s current needs. Repercussions for policy violations can include disciplinary action, suspension, or termination. This ensures that employees are held accountable for their actions and that key control policies are consistently enforced.
Handling Key Requests and Returns
Maintaining a secure environment hinges on the process for submitting key requests and returning keys upon termination of employment or changes in access needs. Key requests should be submitted through the Facilities website by either a Department Head or Administrative Assistant.
A minimum fee of $100 per key will be incurred for not returning keys upon termination of employment or student status.
Using Online Forms and Procedures
The key request and return process can be streamlined by using online forms and procedures. Providing clear instructions, handling errors, and ensuring mobile-friendly design are essential components of effective online forms and procedures.
Additional factors, such as security measures, regular updates, and testing and feedback, contribute to a seamless and user-friendly experience for employees when using online forms and procedures.
Don’t know where to start with the employee dating policy? Read our article on Amazon employee dating policy to lean how to navigate this potentially sensitive aspect of workplace relationships.
Ensuring Timely Return of Keys
Maintaining a secure environment and preventing unauthorized access to restricted areas necessitates the timely return of keys. Optimal practices for guaranteeing a punctual return of keys include:
- Implementing a key tracking system
- Formulating unambiguous policies and procedures
- Issuing reminders
- Executing routine audits
- Imposing consequences
- Preserving open communication.
By taking these measures, organizations can effectively manage their key control systems and maintain a secure environment for all employees.
Summary
In conclusion, crafting a key control policy for employees is essential in ensuring the overall security of your organization. By establishing clear policies, building a master key system, implementing keyholder responsibilities, training employees on key control policies, monitoring and enforcing key control policies, and handling key requests and returns, your organization can create a secure and well-organized access management system. As security remains a top priority for every organization, investing time and resources into an effective key control policy will undoubtedly pay dividends in the long run.
Frequently Asked Questions
What is a key control policy?
A key control policy is an access control system used to ensure that only authorized personnel have access to company keys, thereby enhancing information security and protecting against cybercrime.
What are the responsibilities of key control?
Key control is responsible for issuing and retrieving keys, maintaining records of key distribution and use, conducting key audits, and training an assistant security officer in all aspects of key security.
Proper documentation and tracking of who has been issued a key is vital to ensuring safe and secure access to spaces and assets.
What is the lack of an effective key control policy?
Without a proper key control policy, there is a risk of financial and other losses due to not knowing who has access to facilities, assets, fleets, and staff.
Such disorganization can threaten the security of your organization’s most valuable assets.
What is key control in an organization?
Key control is a critical process of managing physical keys and access to important assets, people, information, and spaces in your organization. It is crucial to ensure the protection of these resources by putting appropriate key control measures in place.
These measures can include key tracking, key registration, key assignment, and key authorization. Key tracking involves keeping a record of who has access to which keys and when. Key registration involves assigning a unique identifier to each key.
What are the main objectives of implementing a key control policy?
The main objectives of implementing a key control policy are to establish protocol for institutional control of keys, outline process for requesting keys, and ensure overall security.