In today’s digital-driven business landscape, IT company policies have become a fundamental pillar for ensuring data security, streamlining processes, and mitigating cyber threats. With the ever-evolving technological landscape and increasing security concerns, it has never been more crucial for organizations to implement comprehensive and effective IT policies. This blog post will explore the importance of IT company policies, essential policies to implement, the development and implementation process, the need for regular review and updates, and real-life examples of successful IT policy implementation.
Key Takeaways
- IT Company Policies are essential for data security, privacy protection, and streamlining business processes.
- Developing comprehensive policies requires engaging stakeholders, customizing templates & ensuring company-wide adoption.
- Regularly reviewing & updating IT policies is key to maintaining effectiveness and preventing liabilities.
The Importance of IT Company Policies
IT policies, while often underestimated, are vital for an organization’s success. They serve as the foundation of all processes and must align with the business’s primary mission and dedication to security. A well-crafted IT policy comprises a clear purpose, a defined scope, and relevant policies and procedures to prevent data breaches. Precise language in these policies is critical in ensuring that all employees comprehend the policy and are able to adhere to it.
To prevent security breaches, it’s necessary to enforce IT policies and ensure all company personnel are aware of and adhere to them. One of the fundamental IT policies is the Acceptable Use Policy (AUP), which outlines the acceptable use of computer equipment for business purposes and defines the parameters of inappropriate use of information systems. Ensuring equitable IT policies for employees is crucial to prevent any demoralization and maintain a secure and efficient working environment.
Failing to adhere to IT policies can lead to repercussions ranging from warnings for minor violations to disciplinary action for more serious violations. The crucial role of IT company policies in ensuring data security, protecting sensitive information, and maintaining efficient operations cannot be overstated.

Data Security and Privacy Protection
IT policies are vital in protecting data and ensuring privacy compliance, preventing potential data breaches. An IT company policy encompass various aspects, including:
- Confidential Information Policy Templates
- Data Integrity Policy
- Acceptable Use Policy
- Data Protection Policy
- Data Use Policy
- Security Awareness and Training Policy
- Email Acceptable Use Policy
- Password Creation and Management Policy
- Data Governance Policy
- Data Retention Policy
- Clean Desk Policy
- Vendor Management Policy
- Social Media Acceptable Use Policy
- Password Policy
- Updating Access Authorization and Modification Policies and Procedures.
To ensure data privacy, regular updates to asset management policies and procedures are necessary. The organization should develop and record a procedure for establishing, documenting, assessing, and altering access to systems and sensitive information, which typically involves HR and IT, who authorize access upon hiring and termination.
Organizations can safeguard their data and ensure privacy compliance in an increasingly interconnected world through the implementation of comprehensive IT policies, thus minimizing the risk of a data breach.
Streamlining Business Processes
IT policies can help standardize processes and maintain consistency across the organization, streamlining business operations. An IT purchasing policy, for example, establishes protocols for the acquisition and implementation of relevant technology. This policy typically includes elements such as:
- The approval process
- Identified vendors
- Approved software
- Standardized configurations
- Responsibility for purchasing and installation
The use of a template for IT policies can minimize discrepancies and misinterpretations by providing a standard format for all IT policies. Implementing well-crafted IT policies, such as an IT purchasing policy, can provide benefits such as improved inventory management, enhanced security, and increased uniformity.
Streamlining business processes through IT policies ultimately enhances efficiency and minimizes idle time.

Mitigating Cyber Threats
In the face of ever-evolving cyber threats, IT policies play a crucial role in mitigating potential damages and reducing risks. It is essential to have policies in place that guarantee the secrecy, accuracy, and availability of confidential data on the organization’s systems and reduce the consequences of an IT security-related incident.
Logging audit events, for example, is beneficial in detecting and restoring compromised data. A security policy can help prevent misuse of information systems, such as when an employee accesses data through a company computer for purposes other than their job duties.
The implementation of robust IT policies allows organizations to effectively mitigate cyber threats and reduce potential damages.
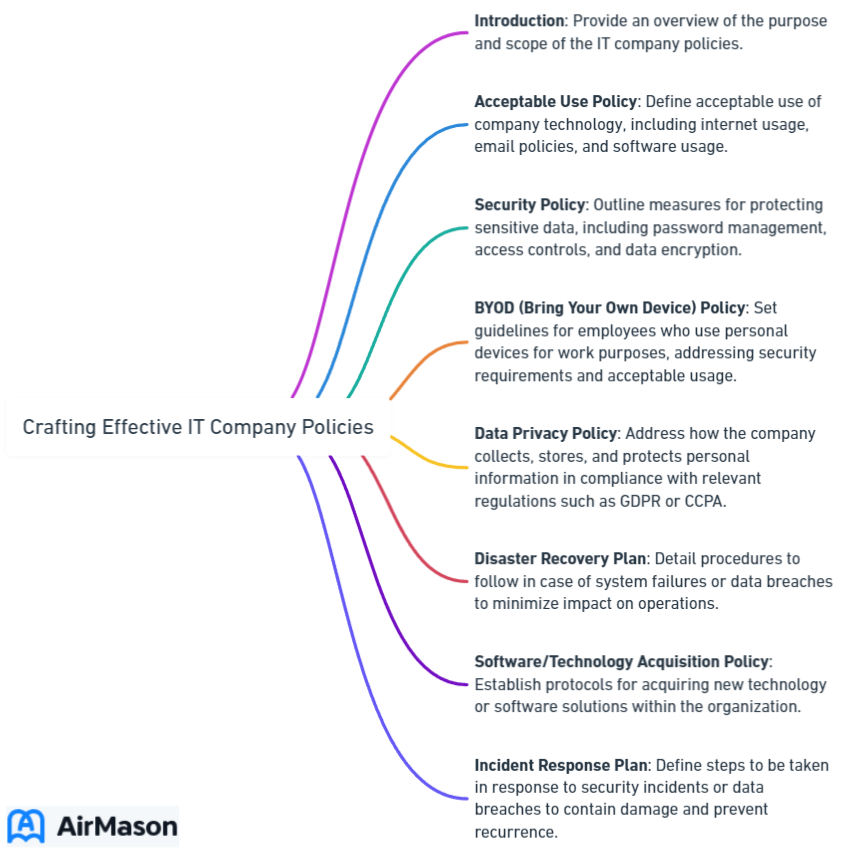
Essential IT Company Policies to Implement
Identifying and implementing key IT policies within an organization is critical for optimal data security and smooth operations. Some essential IT company policies example include:
- Password Security Policy
- Software Usage Policy
- Acceptable Use Policy (AUP)
- Patching Strategy Policy
- Cloud & App Use Policy
An effective Password Security Policy provides employees with guidelines for creating and managing secure passwords, while a Software Usage Policy outlines the applications permissible for installation and use on computer systems and mobile devices owned by the organization. Implementing these software management policies, along with others such as the AUP, Patching Strategy Policy, and Cloud & App Use Policy, ensures a secure and efficient working environment.
Incorporating these essential policies enables organizations to effectively safeguard their data, maintain network security, and reduce the risk of security breaches. A well-rounded IT policy framework not only protects the organization, but also helps streamline processes and address potential security concerns.
Remote Access Policy
The Remote Access Policy is designed to reduce the risk of damage from unauthorized use of resources when connecting to the company’s network from any host. A remote work policy should include measures to ensure the safety and security of online connections. For instance, organizations can mandate that employees exclusively use company computers or virtual private networks (VPN). Such policies are beneficial in mitigating the risks associated with employees accessing sensitive information outside of the office.
Implementing a VPN Use Policy aims to:
- Ensure adherence to security protocols when utilizing a VPN
- Establish a robust Remote Access Policy to regulate remote workers’ access to company resources
- Ensure secure connections
- Enhance overall data security.
Bring Your Own Device (BYOD) Policy
A Bring Your Own Device (BYOD) policy requires the utilization of personal devices for business operations. Implementing a BYOD policy comes with advantages such as cost savings and convenience for employees, but it also presents challenges such as security concerns and uncertainty about reimbursement for personal device use in the workplace.
A well-crafted BYOD policy outlines requirements such as utilizing personal devices on the organization’s network, connecting using a VPN, and performing regular scans for malware. Implementing a BYOD policy allows organizations to leverage the benefits of personal devices while securing company data and ensuring it’s accessible only for authorized use.
Information Security Policy
An effective Information Security Policy is crucial for protecting sensitive data and maintaining network security. This policy should encompass various aspects, including:
- Device Acceptable Use Policy
- Web Acceptable Use Policy
- Email Acceptable Use Policy
- Social Media Acceptable Use Policy
- IT security policies addressing physical security, network security, cyber security and audits, and data security.
The implementation of a comprehensive information security policy enables organizations to effectively shield their data and systems from unauthorized access and malicious attacks. In today’s digital world, having a robust information security policy in place is no longer optional; it is a necessity for maintaining the privacy and integrity of sensitive data and ensuring the continued success of the business.
Especially for small businesses, the importance of implementing a comprehensive information security policy cannot be overstated. While they may not have the same resources as larger enterprises, the threats to their data and systems are just as real. In fact, small businesses can be particularly attractive targets for cybercriminals due to their potentially weaker defenses. Therefore, developing tailored information security policies that are appropriate for the scale and complexity of the business is crucial.
These policies for small business should address areas such as password management, data backup procedures, employee training on cybersecurity best practices, and measures to safeguard customer information. By adopting and adhering to such policies, small businesses can significantly enhance their resilience against cyber threats and demonstrate a commitment to protecting their customers’ trust.
Developing and Implementing IT Company Policies
Creating and executing IT policies within an organization involves several steps, including:
- Articulating the purpose
- Outlining the scope
- Identifying IT policy components
- Evaluating policy enforcement methods and sanctions
The initial step in constructing an IT company policy is to conduct research into the details, ensuring the policy is tailored to the organization’s specific needs and requirements.
The involvement of relevant stakeholders like management, human resources, and IT staff in the policy development process is necessary to ensure all required rules and practices for maintaining data security are incorporated. Customizing policy templates can be beneficial in terms of time and cost savings, as well as ensuring that policies are comprehensive and current.
Clear communication, employee engagement, and training and education are required to ensure company-wide adoption of IT policies. This guarantees accountability and adherence to the policies, resulting in a secure and efficient working environment.
Engaging Relevant Stakeholders
When developing IT policies, it is vital to involve key stakeholders such as IT department, human resources, and management, as their input is invaluable in shaping the policy. Engaging relevant stakeholders is essential for the success of any project or initiative, and it is crucial to understand their needs and expectations, communicate regularly and transparently, involve them in decision-making, and provide opportunities for collaboration.
Involving pertinent stakeholders in the policy development process ensures the organization’s IT policies are comprehensive, current, and tailored to their specific needs. This collaborative approach not only results in more effective policies, but also fosters a sense of ownership and commitment among stakeholders, ultimately contributing to the success of the policy implementation.
Customizing Policy Templates
Using pre-made policy templates can offer numerous advantages, such as cost-effectiveness, expediency, and uniformity. These templates provide important guidelines and rules, ensuring that all IT policies adhere to the same format and are in compliance with current regulations and technology.
Customizing IT policies to suit specific business requirements is essential to guarantee that the policy is tailored to the organization. Adapting pre-made policy templates saves time and resources for organizations, while ensuring their IT policies remain comprehensive, current, and tailored to their unique needs.
Ensuring Company-Wide Adoption
Promoting awareness and adherence to IT policies is essential for their success. Clear communication is imperative, involving elucidating the purpose and significance of the policy, as well as the repercussions of non-compliance. Leadership support is also essential, with leaders demonstrating their dedication to the policy by exemplifying it and providing the necessary resources for compliance.
Employee engagement is crucial for guaranteeing company-wide adoption of IT policies, and it is recommended that employees are included in the formation and execution of the policy, as well as in the assessment and evaluation of its effectiveness. Providing training and education ensures that employees have the requisite data and materials to comprehend and adhere to the policy. Cultivating a culture of compliance and continuous learning enables successful implementation and adoption of IT policies within organizations.

Reviewing and Updating IT Company Policies
Regularly reviewing and updating IT policies is crucial to ensure they remain current and effective. As technology and business needs evolve, it is essential to adapt IT policies to keep up with these changes and maintain the organization’s security and efficiency.
Utilizing IT policy templates can save time and provide guidance, ensuring that policies are comprehensive and in line with current regulations and technology. By conducting regular assessments, involving relevant stakeholders, and updating policy documentation accordingly, organizations can stay ahead of potential security threats and maintain smooth and efficient operations.
Monitoring compliance and effectiveness is an essential part of reviewing and updating IT policies. Implementing a robust monitoring system, conducting regular audits, and providing training and education are all crucial components of this process. Active monitoring and necessary adjustments of IT policies allow organizations to better adapt to changes in technology and regulations, ensuring their business’s continued success and security.
Monitoring Compliance and Effectiveness
To ensure optimal monitoring of compliance and effectiveness, organizations should:
- Establish clear policies and procedures
- Regularly assess and update policies
- Implement a robust monitoring system
- Conduct regular audits
- Provide training and education
- Cultivate a culture of compliance
- Establish reporting mechanisms
- Monitor and analyze data
- Take corrective actions.
Consistent audits and addressing potential issues ensure adherence to policies and necessary adjustments within organizations.
Engaging with stakeholders and evaluating the success of implemented policies is also essential in the monitoring process. By actively tracking policy compliance and evaluating the success of implemented policies, organizations can continuously improve their IT policies, ensuring a secure and efficient working environment.
Adapting to Changes in Technology and Regulations
As technology and regulations change, it is essential for organizations to revise their IT policies accordingly. This helps to safeguard the company from potential liabilities and guarantee that the company is functioning in a secure and efficient manner. Staying informed, conducting regular assessments, fostering a culture of learning, building a flexible IT infrastructure, establishing strong partnerships, developing a robust compliance program, and embracing innovation are all recommended practices for adapting to changes in technology and regulations.
Proactive adaptation to changes in technology and regulations maintains the effectiveness of IT policies and ensures continued business success and security. This forward-thinking approach not only safeguards the organization, but also helps to streamline processes and address potential security concerns.

Case Studies: Successful IT Company Policy Implementation
IT company policies play a crucial role in ensuring data security, organizing business operations, and mitigating cyber risks. Real-life examples of successful IT policy implementation include:
- Remote access policy: enables employees to access company data and resources securely from any location
- Bring Your Own Device (BYOD) policy: allows employees to use their personal devices for work purposes
- Information Security Policy: protects the company’s data and systems from unauthorized access and malicious attacks
Best practices for successful IT company policy implementation include:
- Clear definition of policies
- Effective communication with employees
- Obtaining buy-in
- Providing training and education
- Reviewing and updating policies regularly
- Enforcing policies consistently
- Monitoring and measuring compliance
- Providing support and guidance
- Fostering a culture of compliance
- Continuously improving policies
Following these best practices enables organizations to implement IT policies effectively, fostering a secure and efficient working environment with the right choice of operating systems.
These case studies demonstrate the importance of implementing comprehensive and effective IT policies in organizations across various industries. As a result, companies can significantly enhance their:
- Data security
- Business processes
- Mitigation of potential cyber threats
- Continued success in an increasingly interconnected world.
Summary
In conclusion, IT company policies are of paramount importance for organizations in today’s digital-driven business landscape. Implementing comprehensive and effective policies not only ensures data security and privacy, but also streamlines business processes and mitigates cyber threats. By involving relevant stakeholders, customizing policy templates, ensuring company-wide adoption, and regularly reviewing and updating policies, organizations can maintain a secure and efficient working environment. The real-life examples and best practices shared in this blog post serve as a testament to the positive impact of well-implemented IT policies on businesses across various industries.
Frequently Asked Questions
What are the IT organizational policies?
IT organizational policies provide guidelines for the appropriate use of technology within a company, ensuring that everyone uses resources in a consistent, effective, and efficient manner.
These policies help to ensure that technology is used in a way that is beneficial to the company, and that it is not abused or misused. They also help to ensure that the company’s data is secure and that the company’s intellectual property is protected.
What is an example of an IT policy?
An example of an IT policy is an incident response policy, an access control policy, a record retention and destruction policy, a master data policy, a data classification framework or data sharing policy.
What is IT management policy?
IT Management Policy is the process of creating, communicating and managing rules and guidelines to ensure effective, safe and compliant use of information technology across an organization. It involves setting expectations and directions for creating, capturing and managing information assets such as records, information and data.
Why is it important to involve relevant stakeholders in the policy development process?
Involvement of relevant stakeholders in the policy development process is important to ensure all necessary rules and practices are incorporated, as well as to tailor the policy to the organization’s specific needs.
It is essential to involve stakeholders in the policy development process to ensure that all necessary rules and practices are included and that the policy is tailored to the organization’s specific needs.
What are some essential IT company policies that every organization should implement?
Every organization should implement essential IT company policies such as Password Security Policy, Software Usage Policy, Acceptable Use Policy (AUP), Patching Strategy Policy, and Cloud & App Use Policy.
These policies are designed to protect the organization’s data and systems from unauthorized access, malicious software, and other cyber threats. They also help ensure that employees are using the organization’s IT resources responsibly and in accordance with the organization’s standards.
The Password Security Policy outlines the requirements.